What Is an SSL/HTTPS Proxy: How It Works and When to Use It
An SSL proxy, often called an HTTPS proxy, is an intermediary server that forwards web requests between a user and a website through an encrypted HTTPS connection. Instead of connecting directly to the destination server, the client routes traffic through the proxy, which helps secure data transmission and manage outgoing requests.
Lukas Mikelionis
Last updated: Mar 18, 2026
4 min read
TL;DR
- SSL/HTTPS proxies route traffic through an intermediary server before reaching the destination website.
- Data is protected with TLS encryption, preventing unauthorized interception during transmission.
- The destination server sees the proxy’s IP address, not the user’s original IP.
- Common use cases include web scraping, automation systems, and enterprise traffic management.
- Despite the name, HTTPS proxies rely on TLS, the modern successor to the older SSL protocol.
What Are the Benefits of an SSL / HTTPS Proxy?
SSL proxies, including residential proxies, provide several advantages by routing web traffic through an intermediary server while maintaining encrypted communication with the destination website.
This combination of security and routing flexibility makes them useful for individuals, developers, and organizations working with online services. Here, we have:
Encrypted web traffic
One of the most important advantages of an SSL proxy is the ability to send requests through encrypted HTTPS connections. When a client communicates with a website through a proxy, the data exchanged between both systems is protected by TLS encryption.
In practical terms, this means the information traveling across the network cannot easily be interpreted by someone observing the connection path. For environments that exchange sensitive data or run automated interactions with external services, encryption adds an extra layer of protection.
Additional privacy through IP masking
SSL proxies can also provide an additional layer of privacy by hiding the original client’s IP address, effectively functioning as an anonymous proxy. Instead of connecting directly to a website, the request is first routed through the proxy server, meaning the destination site sees the proxy’s IP address rather than the user’s actual address.
This approach reduces the amount of identifiable network information exposed during the request. When combined with HTTPS encryption, both the transmitted data and the originating address become less visible to outside observers.
For a deeper explanation of the differences between HTTP and HTTPS proxies, see this guide.
Safer automation and data collection
Many automated systems interact with websites on a large-scale. Tools such as web scraping frameworks, monitoring platforms, and data collection pipelines often send large numbers of requests to external services.
Using an HTTPS proxy allows these requests to travel through encrypted connections while still benefiting from proxy routing. This helps protect request data and provides a more controlled way to manage automated traffic.
For teams building data pipelines or monitoring infrastructure, SSL proxies provide a practical way to maintain secure communication with external websites.
How do SSL/HTTPS proxies work?
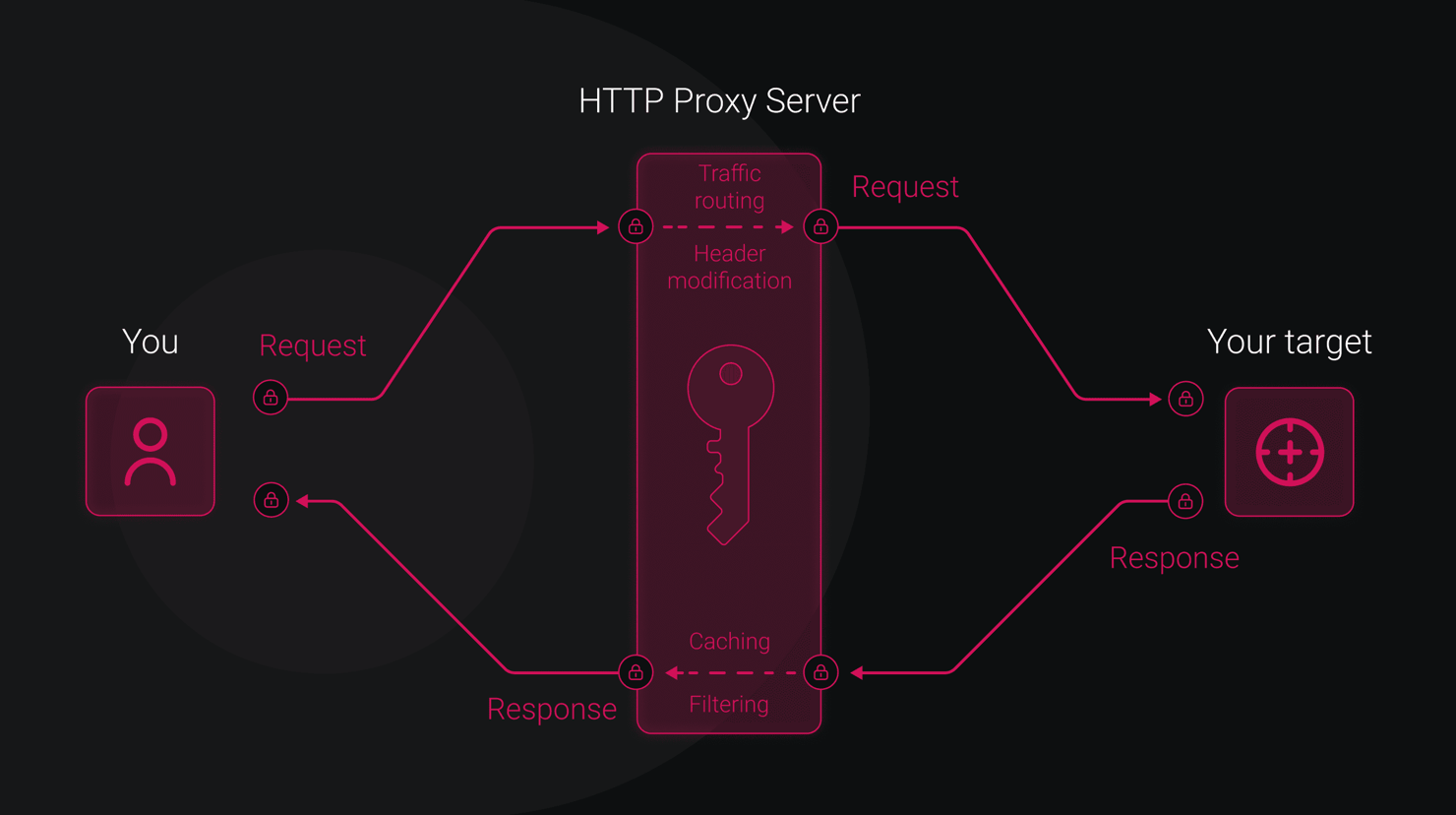
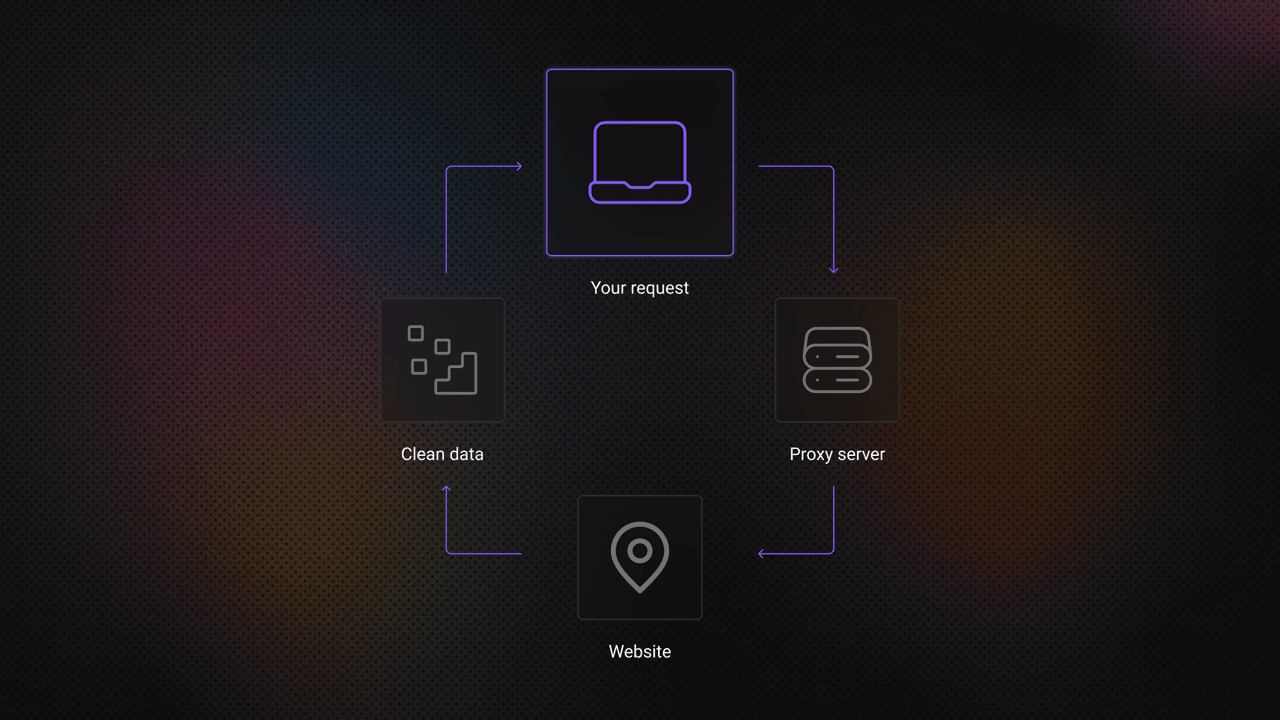
To understand how an SSL proxy works, it helps to look at how a secure request travels from a client to a destination server.
When an HTTPS proxy is used, the proxy server sits between the client and the target website, forwarding traffic while allowing the encrypted session to remain intact. Most modern browsers display a warning when a website does not have a valid SSL certificate.
In most situations, the connection unfolds in a series of steps:
- The client asks the proxy to open a connection. The process begins when a client application, such as a web browser, script, or automation tool, asks the proxy server to connect to a specific website. The request includes the destination domain and the port to be used, which is typically port 443 for HTTPS traffic.
- The proxy connects to the destination server. After receiving the request, the proxy establishes a network connection to the target server. At this point, the proxy simply acts as a relay between the client and the destination website.
- A secure TLS session is established. Once the connection path exists, the client and the destination server begin negotiating a secure session using Transport Layer Security (TLS). During this stage, both sides exchange the information needed to create an encrypted communication channel.
- Encrypted traffic flows through the proxy. After the TLS session is established, the client starts sending HTTPS requests. These encrypted data packets pass through the proxy on their way to the destination server. Because the traffic is encrypted, the proxy generally forwards the data without inspecting its contents.
- The server returns the response. The destination server processes the request and sends the response back along the same path. The proxy relays the encrypted response to the client, completing the request cycle. Through this process, the proxy routes traffic between the client and the server, while the encryption protects the data being exchanged.
How do forward and reverse SSL proxies differ?
SSL proxies can be deployed in two main ways: forward proxies and reverse proxies. The difference lies in which side of the connection the proxy represents.
Forward SSL proxy
A forward proxy sits between users and the internet. Requests from internal devices are sent to the proxy first, which then forwards them to external websites.
Organizations often use forward proxies to manage outbound traffic, enforce security policies, or inspect encrypted connections as needed.
Reverse SSL proxy
A reverse proxy sits in front of one or more web servers. Incoming requests from the internet first reach the proxy, which then directs them to the appropriate backend service.
Reverse proxies are frequently used for SSL termination, where the proxy handles encryption and decryption before forwarding requests internally. The processing strain on application servers is lessened as a result.
Core Methods Used by SSL Proxies
Depending on their configuration, SSL proxies can handle encrypted traffic in several ways. Considering the following:
SSL pass-through
In this configuration, the proxy simply forwards encrypted traffic between the client and the server without decrypting it. The proxy acts purely as a relay.
SSL termination
With SSL termination, the encrypted session ends at the proxy. The proxy decrypts the traffic and forwards it to the backend server, often through a secure internal network.
SSL bridging (inspection)
In this setup, the proxy decrypts incoming traffic for inspection and then establishes a new encrypted connection to the destination server. This approach is often used in enterprise security environments.
Where can you use an SSL / HTTPS proxy?
SSL proxies are used in many technical environments where encrypted communication and controlled traffic routing are both important.
Web data collection
Data collection systems often rely on HTTPS proxies to interact with websites securely while distributing requests across multiple network addresses. Using a shared proxy infrastructure can be especially useful in these scenarios, as it allows analysts and researchers to rotate across large pools of HTTPS IP addresses when gathering public web data.
Access to a broad range of proxy endpoints helps maintain stable connections, reduce the likelihood of request blocking, and support large-scale data collection workflows.
Security inspection
Organizations may use SSL proxies to analyze encrypted outbound traffic and detect potential threats hidden inside HTTPS connections.
Infrastructure performance optimization
Reverse proxies can handle encryption tasks at the network edge, reducing the workload on backend servers that would otherwise manage large numbers of TLS handshakes.
Ad verification and monitoring
Advertising platforms use encrypted proxy connections to verify how campaigns appear in different geographic regions while maintaining secure browsing sessions.
Privacy-focused access
In restricted network environments, routing traffic through an SSL proxy can help limit the visibility of browsing destinations to local network providers.
Residential proxies with #1 response time
Plug 115M+ IPs into your workflows and easily avoid CAPTCHAs, IP bans, or geo-restrictions.
When should you use an SSL proxy?
SSL proxies are most useful in situations where both secure communication and traffic routing control are required.
Organizations often deploy them when building automation platforms, collecting public web data, managing controlled browsing environments, or protecting backend infrastructure through reverse proxy deployments.
Because most modern websites rely on HTTPS, proxies that support encrypted traffic have become an essential part of many networking and data-driven systems.
Decodo proxy solutions support HTTPS connections across residential proxy, ISP, and datacenter networks, enabling encrypted traffic to be routed while selecting the infrastructure that best fits your operational needs.
About the author

Lukas Mikelionis
Senior Account Manager
Lukas is a seasoned enterprise sales professional with extensive experience in the SaaS industry. Throughout his career, he has built strong relationships with Fortune 500 technology companies, developing a deep understanding of complex enterprise needs and strategic account management.
Connect with Lukas via LinkedIn.
All information on Decodo Blog is provided on an as is basis and for informational purposes only. We make no representation and disclaim all liability with respect to your use of any information contained on Decodo Blog or any third-party websites that may belinked therein.