Hide IP
An Internet Protocol (IP) address is the most common piece of info to identify a device online. And there may be a lot of reasons why you'd wanna hide it, including protection of your identity and sensitive data, avoiding a digital footprint, bypassing content filters, bans, and all that jazz. Well, don't sweat, buddy – you can cover your IP in many ways!
14-day money-back option

How to Use a Proxy With node-fetch: Setup, Rotation, and Troubleshooting Guide
Justinas Tamasevicius
Last updated: May 26, 2026
9 min read

What Is a Mobile Proxy? How It Works, Uses, and When to Use One
Robertas Lisickis
Last updated: May 07, 2026
10 min read
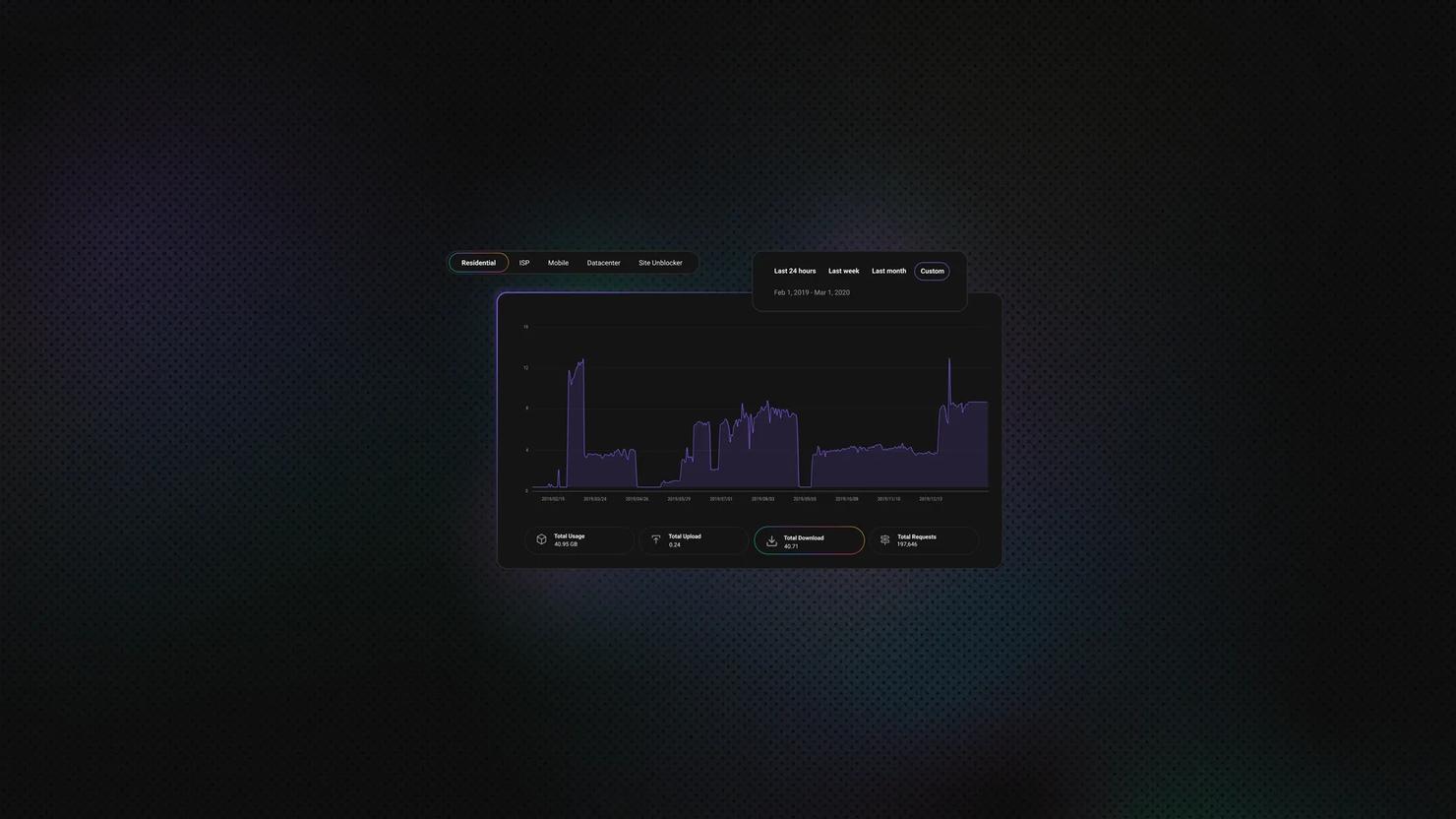
Residential vs Datacenter Proxies: Which Should You Choose?
At first glance, residential and datacenter proxies may seem the same. Both types act as intermediaries that hide your IP address, allowing you to access restricted websites and geo-blocked content. However, there are some important differences between residential and datacenter proxies that you should know before making a decision. We’re happy to walk you through the differences so you can choose what's right for you.
Vilius Sakutis
Last updated: Apr 22, 2026
7 min read
How to Use a Proxy for Telegram: Setup Guide for Android, iOS, Desktop, and Web
Telegram is a popular messaging platform, but it doesn’t come without privacy, security, speed, and availability challenges. To overcome these, you may opt to use a proxy for Telegram. If you’re in the market for a proxy that will be a perfect match for this platform, here is a full guide that explains when and why you’d need a proxy, available types, step-by-step setup instructions, troubleshooting, and security tips to access the app anywhere safely.
Justinas Tamasevicius
Last updated: Mar 19, 2026
9 min read
What Is an SSL/HTTPS Proxy: How It Works and When to Use It
An SSL proxy, often called an HTTPS proxy, is an intermediary server that forwards web requests between a user and a website through an encrypted HTTPS connection. Instead of connecting directly to the destination server, the client routes traffic through the proxy, which helps secure data transmission and manage outgoing requests.
Lukas Mikelionis
Last updated: Mar 18, 2026
4 min read
How to Find Proxy Server Address On Any Device
A proxy server sits between your device and the internet and routes your traffic through an intermediary IP. It's core infrastructure for privacy, access control, and large-scale data operations. If you need to locate your proxy address and port, to set up a scraper, debug a failed connection, or audit your network, you'll want to know exactly where each platform stores these details. This guide covers every major OS, browser, and device, step by step.
Kipras Kalzanauskas
Last updated: Mar 17, 2026
6 min read
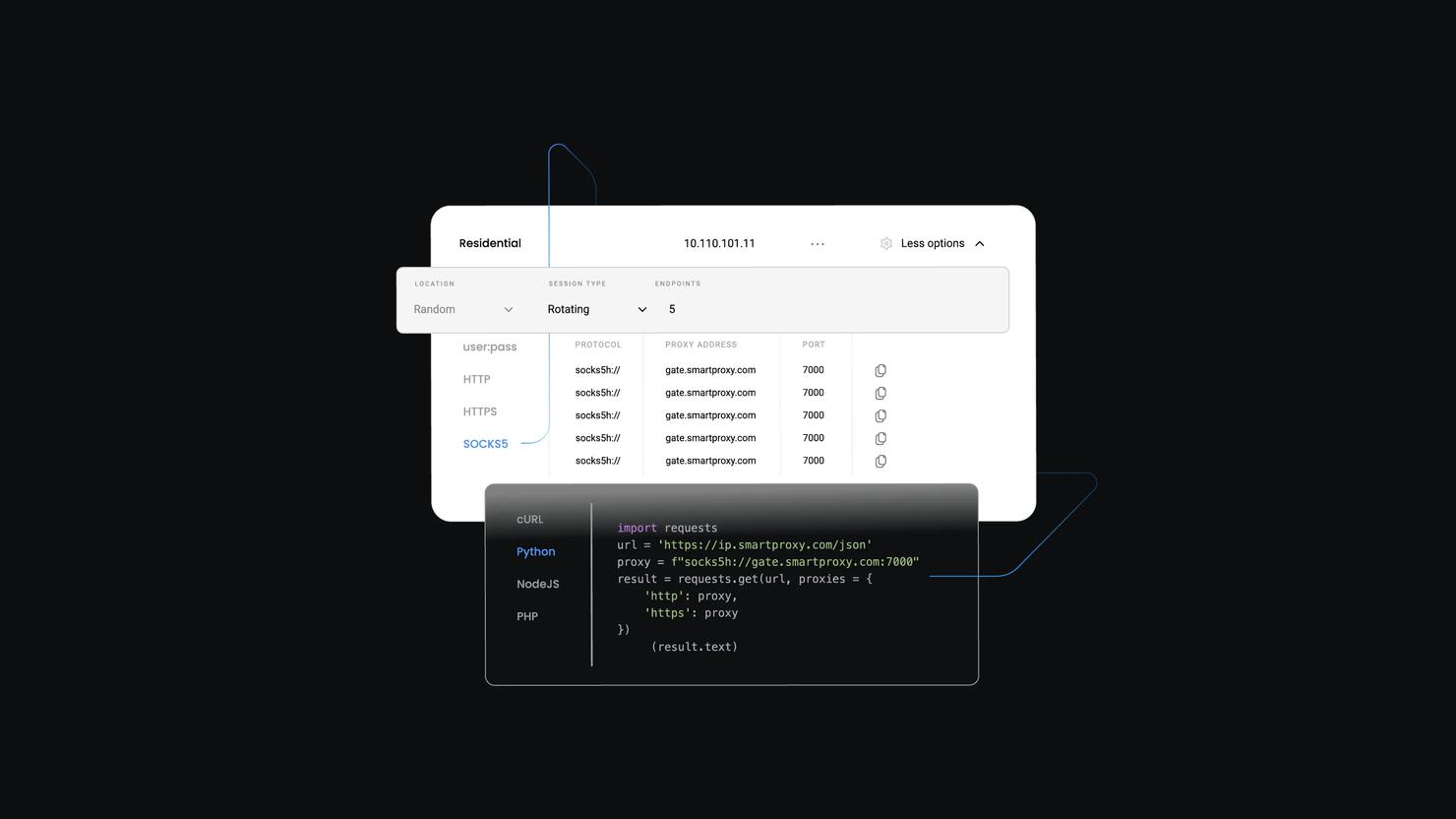
How to Set Up and Use SOCKS5 Proxy
Dominykas Niaura
Last updated: Feb 26, 2026
10 min read
Proxy Anonymity Levels: Transparent vs Anonymous vs Elite
Not all proxies actually protect your identity. Some proxies openly tell websites, "This request came through a proxy," while some can even leak your real IP if they're configured poorly. There are three proxy anonymity levels: transparent, anonymous, and elite. This article will walk you through each one, explain how they work, and help you choose the most suitable option for you.
Vytautas Savickas
Last updated: Feb 20, 2026
7 min read
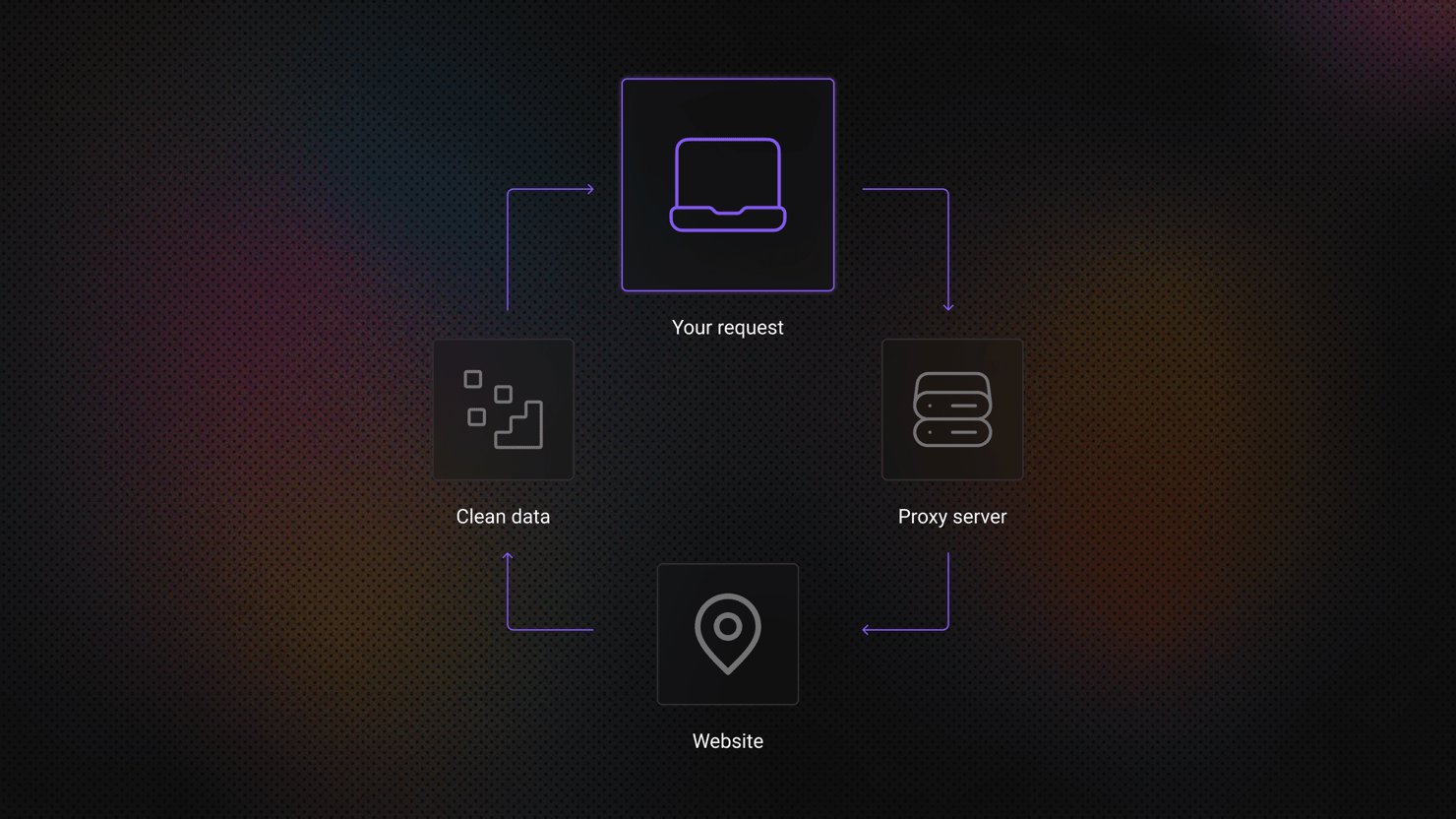
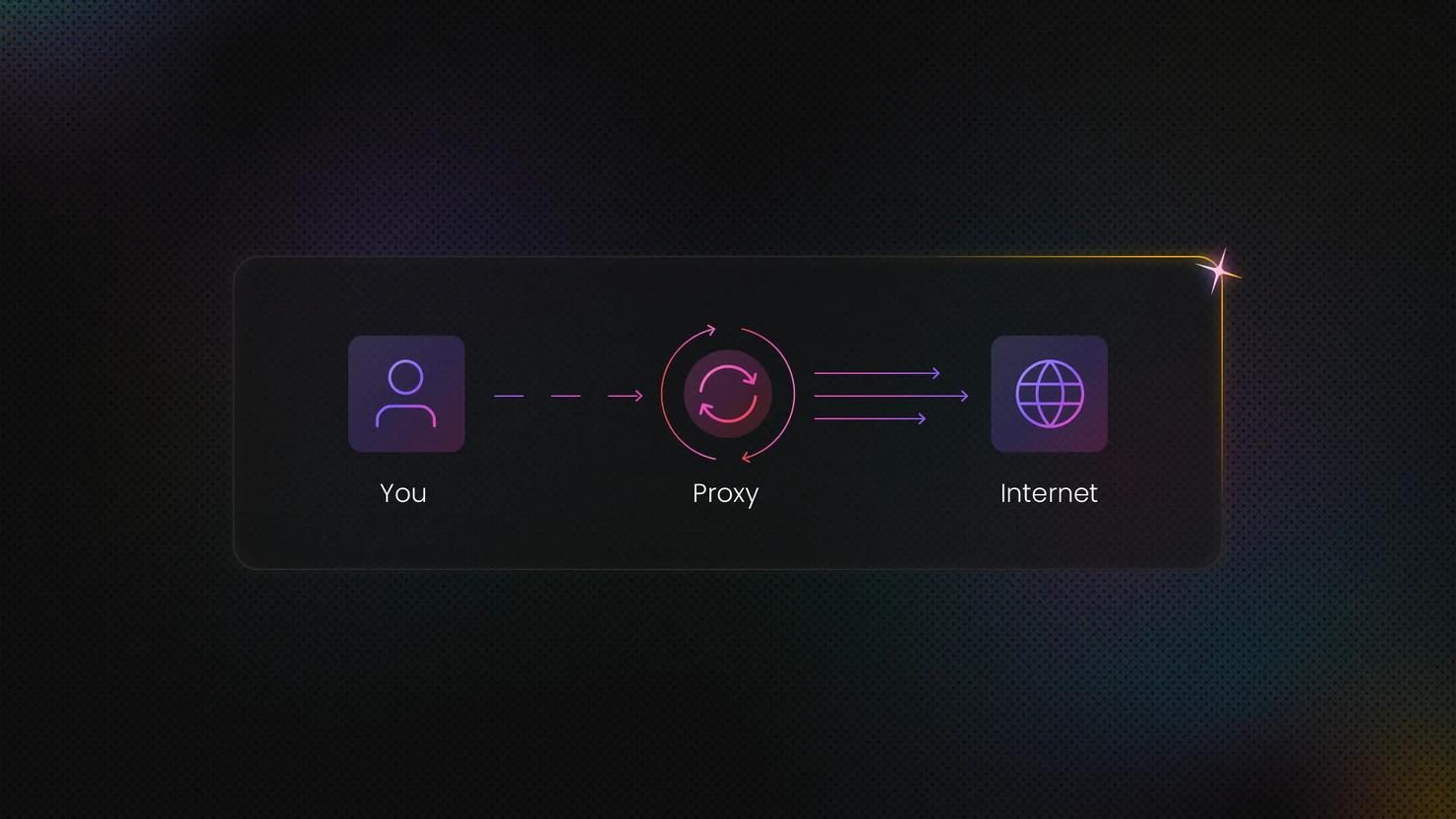
What Is a Proxy Server? How It Works, Types, and Use Cases
TL;DR: A proxy server acts as an intermediary between your device and the internet, masking your IP address and routing your requests through alternative IPs. Businesses use proxies to bypass geo-restrictions, avoid blocks and CAPTCHAs, scrape web data at scale, verify ads, monitor prices, and maintain online anonymity. With the proxy market projected to reach USD 3.12 billion by 2032, understanding which proxy type fits your needs can make the difference between seamless data collection and constant roadblocks.
Mykolas Juodis
Last updated: Feb 12, 2026
8 min read
What Is a Backconnect Proxy? A Complete Guide in 2026
Whether you call yourself a seasoned proxy user or just starting to leverage the power of proxies, it's always good to learn a thing or two. And this time, we're talking about backconnect proxies. In short, backconnect proxies allow you to remain anonymous while accessing the internet by constantly rotating your IP address. These proxies are useful for individuals or companies who need to navigate internet restrictions, monitor competitors, or run web scraping tools.
In this guide, we'll explore everything you need to know about backconnect proxies, how they work, and what benefits you're in for. Shall we begin?
Vytautas Savickas
Last updated: Jan 07, 2026
6 min read
Fake IP Address: What Is It and Why Shouldn't You Use It?
When we scale businesses, do research, or just scroll leisurely, it's always a good idea to be clued up on online security. Whatever your reasons for running your eyes over a web browser are, anonymity and privacy are two pretty important players here. The thing is that any browser, website, system, or network can see our IP address. Some of them might even log your IP address and track it. In this blog post, we’ll go over the dangers of using free software, fake IPs, and the illegal aspects of using IP information.
Benediktas Kazlauskas
Last updated: Nov 05, 2025
6 min read
Random IP Address: Examples, Use Cases, Risks, and Alternatives
From web scraping to getting around geo-blocks, IPs play a huge role in how the internet works behind the scenes. But there’s a flip side – using a free or random IP from a sketchy provider can cause way more trouble than you’d expect. It can break compliance rules, mess with your data, or even lead to bigger operational and reputational problems. Dive into this article to learn more about the risks of random IP addresses.
Kotryna Ragaišytė
Last updated: Aug 19, 2025
8 min read
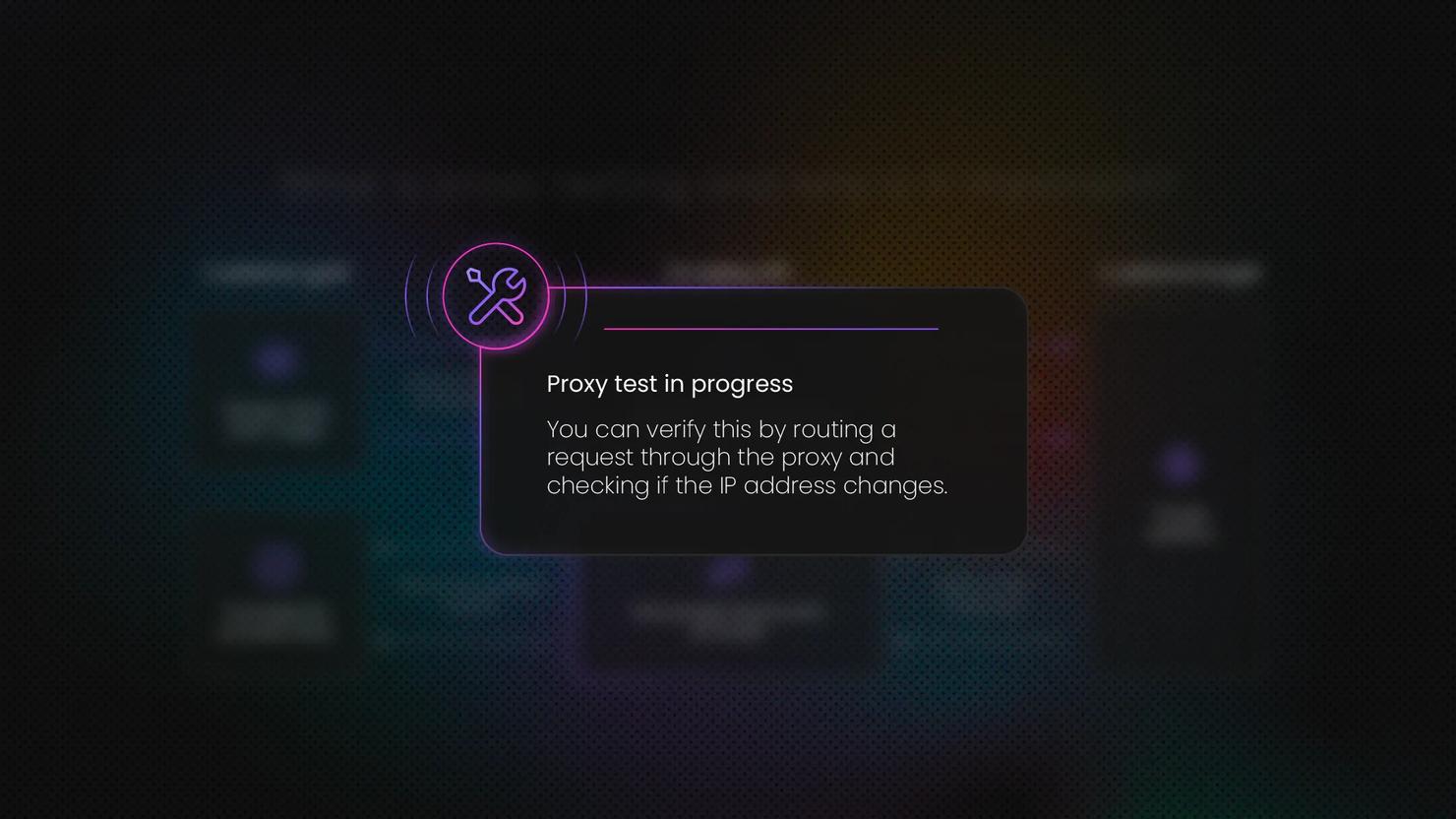
How to Test Proxies: A Complete Guide
Proxies act as intermediaries between your device and the internet, helping mask your IP, bypass geo-restrictions, and enable tasks like web scraping. But some proxies are slow, easily blocked, or insecure. That’s why in this blog post, we’ll show you how to test proxies to ensure they deliver the performance, reliability, and anonymity your use case demands.
Dominykas Niaura
Last updated: Jun 20, 2025
10 min read

What Is a Dedicated Proxy? Key Types & Benefits
Ever feel like you're sharing a slow lane on the information highway? Standard proxies act as intermediaries, masking your IP address for privacy or accessing geo-specific web data. But when performance and a clean reputation matter most, dedicated proxies step in as a powerful solution offering exclusive access, speed, and stability tailored to your needs.
Lukas Mikelionis
Last updated: May 06, 2025
4 min read
What Are Rotating Proxies? Types, Benefits & Use Cases
A rotating proxy is a proxy server that automatically assigns a new IP address at regular intervals or after each connection. In this guide, we'll delve into how rotating proxies work, the different types available, and the most common use cases where they offer a clear advantage.
Dominykas Niaura
Last updated: Apr 30, 2025
7 min read
SOCKS Proxy Explained: Definition, Benefits & Use Cases
A proxy protocol is a set of rules that govern how internet traffic is intercepted, routed, and processed between clients and servers. When it comes to widely used proxy protocols, HTTP often steals the spotlight, leaving SOCKS proxies overlooked despite their flexibility. To help you decide if SOCKS proxies are right for your needs, this blog post will break down what they are, explain how they differ from other proxy types, explore their benefits and drawbacks, and look at the most common use cases.
Dominykas Niaura
Last updated: Mar 14, 2025
10 min read
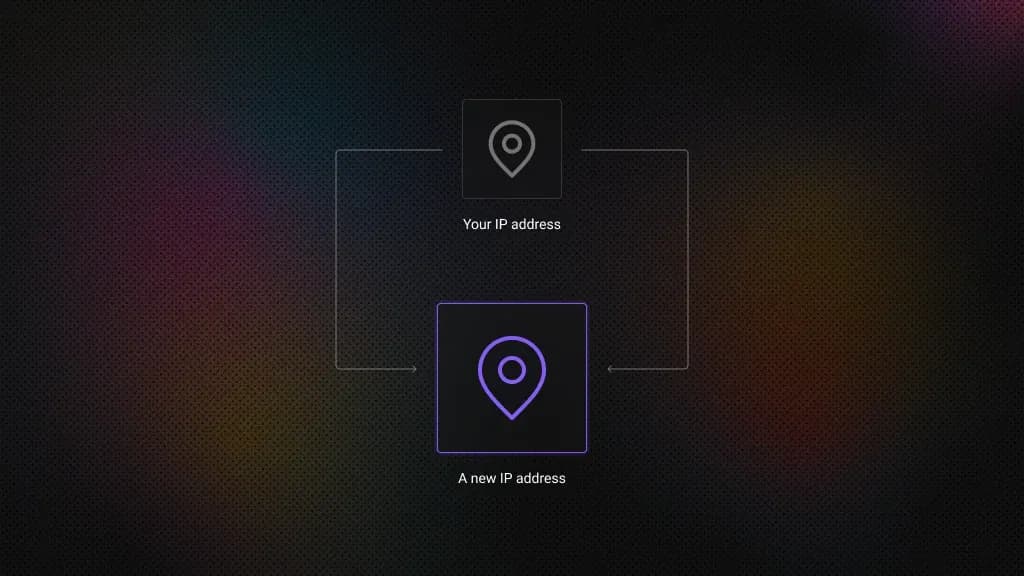
How to Hide Your IP Address: Top 5 Ways
Because the internet never forgets and every click leaves a digital footprint, hiding your IP address is sometimes essential. Staying anonymous enhances data security and grants access to geo-restricted content, though it comes with a few trade-offs. This guide covers 5 effective ways to hide your IP and protect your online privacy.
Vilius Sakutis
Last updated: Mar 07, 2025
7 min read
Difference Between SOCKS5 Proxy vs. HTTP Proxy
Choosing the right proxy type is essential for optimizing performance, security, and efficiency in web data collection. SOCKS and HTTP proxies serve different technical needs, from handling large-scale web scraping projects to managing automation and secure connections. In this article, we’ll compare SOCKS (SOCKS5 in particular) and HTTP proxies, explore their advantages, and help you determine which option best supports your data-driven tasks. By the end, you’ll have the clarity to make an informed decision and scale your operations with confidence.
Vilius Sakutis
Last updated: Mar 06, 2025
7 min read
